Full vulnerability reports provide your organization with an accurate and comprehensive view of your risk profile. The service includes scheduled and on-demand vulnerability scanning capability against the latest known vulnerabilities. Various network devices, such as servers, appliances, applications, and workstations, can be scanned for vulnerabilities.
Get a quote
Hitachi Systems Security’s ArkAngel platform allows you to perform targeted or network-wide vulnerability scans to anticipate and prevent common system vulnerabilities.
Our online ArkAngel risk management platform offers a host of options to give you the flexibility to easily schedule recurring vulnerability scans in advance or conduct scans on demand.
Our consolidated vulnerability reports help you demonstrate compliance with external and internal regulations.
Patching is transformed from an arduous Patching is transformed from an arduous reactive game of scanning, assessing, and implementing every 60-90 days to a proactive risk management process of applying critical patches to high-value systems efficiently and effectively.
The ArkAngel platform maintains a database of known vulnerabilities that will be leveraged to eliminate these vulnerabilities from your environment.
Vulnerability scans are run on a regular basis to identify any gaps in your environment that may be targeted by attackers.
Executive-level and detailed reports are generated to provide a clear view of the evolution of your organization’s security posture over time.
Recommendations and insights are provided to identify opportunities to fortify your overall security posture cost-effectively. Automated recommendations are generated for vulnerabilities that need urgent mitigation depending on the client's confidentiality, integrity, and availability levels.
Generate reports about top 10 vulnerable hosts, vulnerability by services and asset groups, and get a remediation strategy developed by our information security specialists.
Tactical component that reports in real time and measure indicators that have the purpose of guiding the customers towards the best patching strategy to apply in their infrastructure.
Managed Vulnerability Assessment Program
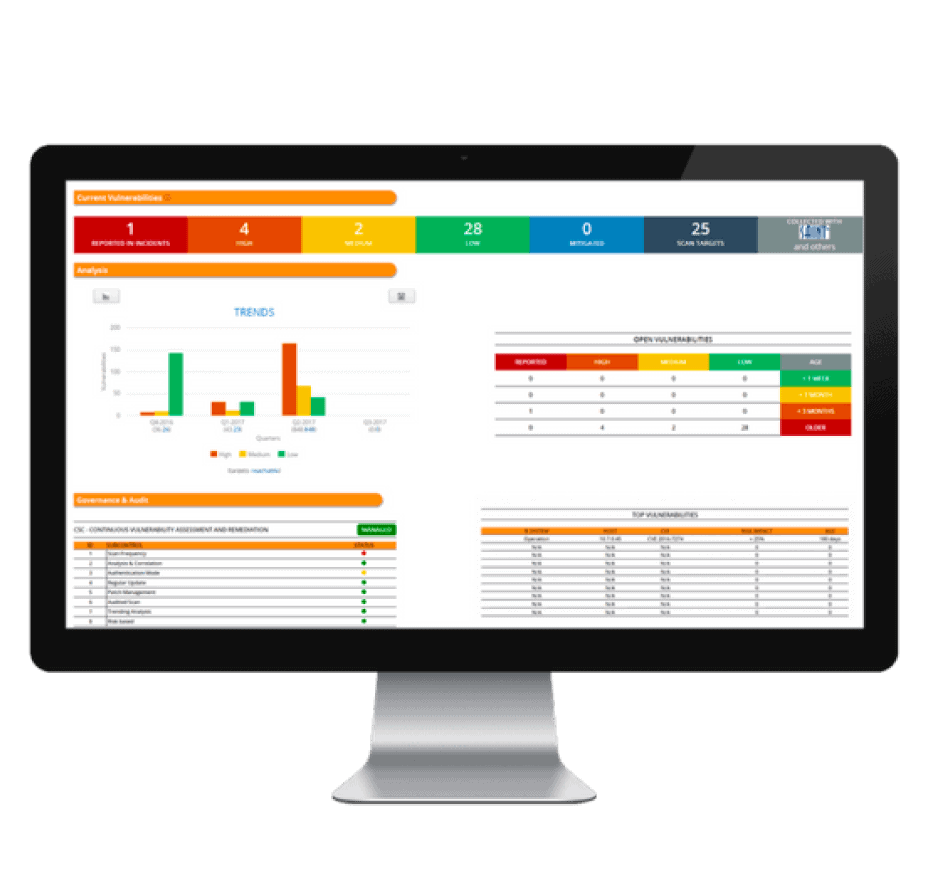
The Vulnerability Management Dashboard provides organizations with real-time analytics of the vulnerabilities scanned in their environment. The dashboard compiles the asset vulnerabilities detected in the network and extracts risk-related indicators and security incidents created by our analysts.
Our exclusive management dashboard lists the top vulnerabilities that would expose your organization to highest risks and what should be fixed first to avoid attacks.
Run monthly reports based on statistics and indicators generated by scanners such as Nessus, MacAfee or Saint and compare over time trends.