The estimated reading time is approximately 2 minutes.
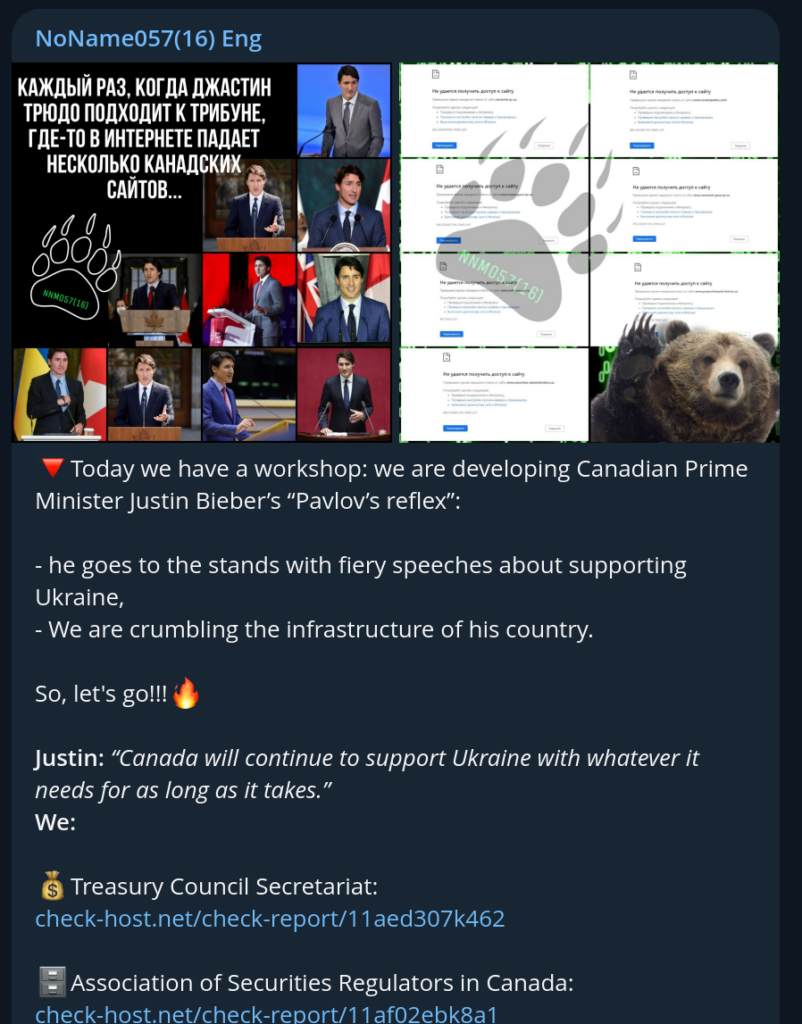
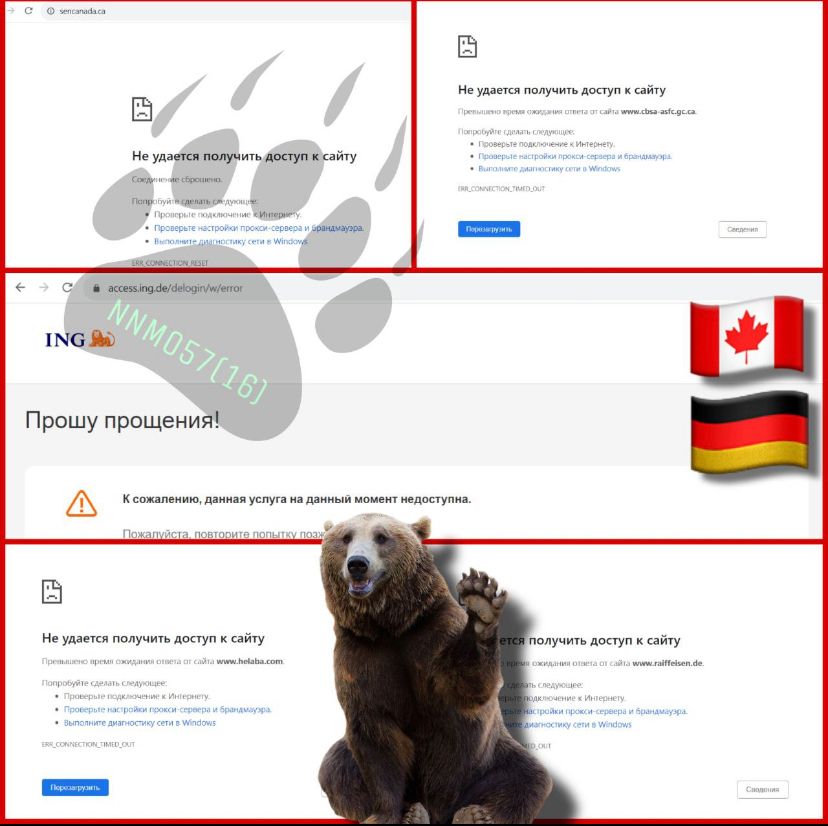
Just months after the initial wave of Distributed Denial of Service (DDOS) attacks that began in early 2023, Canada has again found itself amidst digital aggression. The recent wave commenced on September 13th, leaving several crucial government and regulatory websites crippled over two days.
The affected websites, detailed below, include major entities from the Treasury Council Secretariat to provincial government websites like British Columbia.
Russian hacktivist groups are reportedly behind these attacks, specifically protesting Canada’s support for Ukraine. Significantly, the so-called DDOSia project, led by the elusive NoNames056(16), amplifies these attacks. DDOSia, an attack toolkit, offers individualized configurations to participants, incentivizing them with cryptocurrency payouts.
Contrary to the overt disruptions they cause, DDoS attacks aren't inherently destructive. Instead, their potency lies in their ability to overwhelm and divert, potentially acting as a smokescreen for more nefarious activities. By flooding servers with requests from bot-infested devices, they can knock a website offline or significantly impair its speed and responsiveness.
The politically charged motives underlying these attacks suggest that more are on the horizon.
For the institutions at risk, and indeed, for businesses and services everywhere, understanding and preparing for such assaults is vital.
Basic steps include:
This episode is a stark reminder as the Canadian government scrambles to restore normalcy. In an era where geopolitical tensions can manifest in the digital realm, the importance of cybersecurity cannot be overstated.
If you would like more insights on the DDOSia project and the figures behind it, you can visit Sekoia's analysis.